Ranking on page one used to feel like a big win. Today, it’s the bare minimum. Competitive SERPs are packed with featured snippets, AI overviews, videos, local packs, and heavily optimized competitors fighting for the same clicks. To consistently win visibility, SEO framework agencies don’t rely on isolated tactics—they build layered strategies that stack authority, relevance, and technical strength over time. This five-layer model is the foundation many high-performing agencies use to outperform competitors in even the toughest niches. Each layer builds on the one beneath it, creating momentum that’s difficult for others to replicate.
Layer 1: Technical Infrastructure That Scales

Every strong SEO strategy starts with a solid technical base. Without it, content and backlinks won’t reach their full potential. Agencies begin by optimizing crawlability, indexation, site speed, mobile usability, and structured data. Clean URL structures and logical site hierarchies ensure search engines can easily understand the site. This foundation is critical for long-term SEO success because technical weaknesses compound over time. A slow, disorganized website might rank temporarily, but it will struggle to maintain performance as content expands. Agencies that prioritize infrastructure early create scalable environments where future growth doesn’t require constant clean-up.
Layer 2: Search Intent Mapping
Once the technical layer is solid, agencies move into deep search intent analysis. Instead of targeting keywords in isolation, they map entire keyword ecosystems. Informational, navigational, commercial, and transactional queries are grouped strategically to align with the buyer’s journey. This prevents cannibalization and ensures each page has a clear purpose. Competitive SERPs reward relevance, and intent mapping sharpens that relevance. By structuring content around real user needs rather than just search volume, agencies improve engagement metrics that reinforce rankings over time.
Layer 3: Authority-Driven Content Architecture

Publishing content randomly is a fast way to dilute authority. Framework agencies design structured content ecosystems built around pillar pages and supporting clusters. Each piece strengthens topical depth and connects logically through internal linking. This architecture sends strong authority signals to search engines. Instead of scattered articles competing against each other, the site presents a unified, expert-level resource on its core topics. As competitors chase individual keywords, layered agencies build comprehensive topic ownership, which is much harder to displace in competitive SERPs.
Layer 4: Strategic Authority Building
Backlinks still matter—but modern authority building is far more strategic than mass outreach campaigns. Agencies focus on earning links through digital PR, thought leadership, partnerships, and link-worthy assets like original research or tools. The goal isn’t volume; it’s relevance and trust. High-quality links pointing to well-structured content amplify the previous layers. When technical optimization, intent alignment, and content architecture are already strong, each authoritative backlink has a multiplying effect. This synergy is what helps agencies push clients into top positions in crowded industries.
Layer 5: Conversion and UX Optimization

Ranking alone doesn’t win competitive markets—conversions do. The final layer focuses on user experience, engagement, and conversion rate optimization. Agencies analyze behavior flow, heatmaps, and on-page interactions to refine layout, messaging, and calls to action. When users stay longer, interact more, and convert at higher rates, positive behavioral signals reinforce search performance. At the same time, businesses see measurable ROI from increased organic visibility. This layer ensures traffic growth translates into real business impact rather than vanity metrics.
Winning competitive SERPs isn’t about quick hacks or chasing algorithm updates. It’s about stacking the right elements in the right order. Technical infrastructure supports intent mapping. Intent mapping strengthens content architecture. Content architecture amplifies authority building. Authority fuels visibility. And optimized user experience turns visibility into revenue.…
Read More












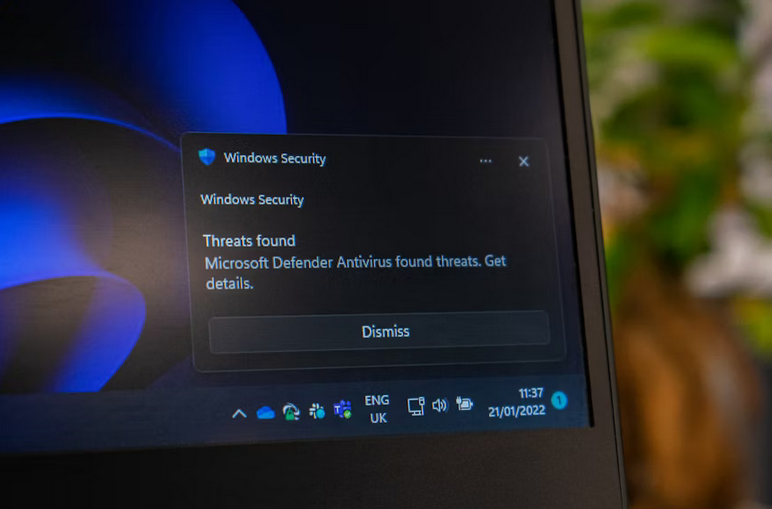










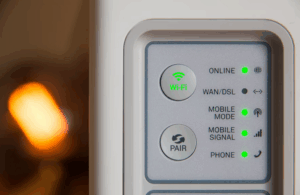 Your router’s internal software, known as firmware, requires occasional updates, just like your computer or smartphone. These updates fix bugs, patch security issues, and sometimes enhance performance. Log into your router’s settings (usually accessible via a web browser) and check for available updates. Also, consider scheduling a router reboot every couple of weeks. This clears cached data and helps the device function more efficiently. It’s a simple practice that often goes ignored but can lead to better connectivity and fewer slowdowns.
Your router’s internal software, known as firmware, requires occasional updates, just like your computer or smartphone. These updates fix bugs, patch security issues, and sometimes enhance performance. Log into your router’s settings (usually accessible via a web browser) and check for available updates. Also, consider scheduling a router reboot every couple of weeks. This clears cached data and helps the device function more efficiently. It’s a simple practice that often goes ignored but can lead to better connectivity and fewer slowdowns.









 Diginytt testing is a rigorous process that ensures smart locks meet high-security standards. This certification focuses significantly on encryption methods used in the devices. Encryption protects data transmission between the lock and the connected devices. It prevents unauthorized access, ensuring that only approved users can control or monitor their locks remotely. Tamper-proofing is another critical aspect of Diginytt evaluation. Smart locks undergo tests to determine how well they resist physical attacks, such as forced entry or tampering attempts. A robust design makes it difficult for intruders to bypass the locking mechanism. These evaluations assure homeowners that their security systems are not just convenient but also reliable against modern threats.
Diginytt testing is a rigorous process that ensures smart locks meet high-security standards. This certification focuses significantly on encryption methods used in the devices. Encryption protects data transmission between the lock and the connected devices. It prevents unauthorized access, ensuring that only approved users can control or monitor their locks remotely. Tamper-proofing is another critical aspect of Diginytt evaluation. Smart locks undergo tests to determine how well they resist physical attacks, such as forced entry or tampering attempts. A robust design makes it difficult for intruders to bypass the locking mechanism. These evaluations assure homeowners that their security systems are not just convenient but also reliable against modern threats.

 In many countries, it’s a criminal offense to be found in possession of a stolen item. Note that iPhones are preferred for their anti-theft features that are activated through the “Find My iPhone app.” An iPhone owner can use this app to lock it and make it useless to the illegitimate owner from halfway around the world.
In many countries, it’s a criminal offense to be found in possession of a stolen item. Note that iPhones are preferred for their anti-theft features that are activated through the “Find My iPhone app.” An iPhone owner can use this app to lock it and make it useless to the illegitimate owner from halfway around the world. Some companies are dedicated to all things iPhone. This means that you can have the phone’s battery or screen replaced. You can as well have it unlocked irrespective of whether you have full details from the previous owner(s) or not. The services come at a cost, but you will be able to use the device without any limitations.
Some companies are dedicated to all things iPhone. This means that you can have the phone’s battery or screen replaced. You can as well have it unlocked irrespective of whether you have full details from the previous owner(s) or not. The services come at a cost, but you will be able to use the device without any limitations.